In the modern cloud-native landscape, security is no longer an afterthought—it is the foundation. Having watched the industry evolve from physical data centers to virtual machines and now to massive containerized orchestrations, I can tell you that the complexity of Kubernetes brings unique risks. The Certified Kubernetes Security Specialist (CKS) is the gold standard for proving you can defend these environments against sophisticated modern threats. This guide is designed for engineers and managers who want to move beyond basic orchestration and master the art of securing the entire container lifecycle. It bridges the gap between simply “making it work” and “making it resilient” against real-world exploits.
What it is
The CKS is an advanced-level certification focusing on the best practices for securing Kubernetes clusters across the entire stack. It covers everything from hardening the underlying host OS to securing the container supply chain and monitoring runtime threats in real-time. It is essentially a masterclass in implementing “Defense in Depth” within a cloud-native ecosystem.
Who should take it
This is specifically for experienced Kubernetes administrators, Security Engineers, and DevSecOps professionals who already hold a valid CKA. If you are responsible for the integrity of production clusters or are leading a digital transformation, this certification is your mandatory next step to ensure compliance and safety. It’s also highly valuable for Architects who need to design secure, multi-tenant infrastructures.
Skills you’ll gain
- Cluster Setup Hardening: You will learn to restrict access to the API server using RBAC, secure the ETCD database with encryption, and manage secrets effectively.
- System Hardening: Master the art of reducing the attack surface by minimizing the host OS, using kernel-level security modules like AppArmor and Seccomp, and restricting kernel access.
- Microservice Isolation: Gain expertise in using Network Policies to prevent lateral movement and implementing mTLS via Service Meshes to secure service-to-service communication.
- Supply Chain Security: Learn to scan container images for vulnerabilities, sign artifacts for integrity, and use Admission Controllers to block the deployment of insecure workloads.
- Runtime Security: Develop skills in detecting anomalies and suspicious behavior using tools like Falco, and learn how to audit logs to identify potential breaches post-event.
Real-world projects you can do after CKS
- Implementing Zero-Trust Architecture: You will be able to design a cluster where no user or service is trusted by default, regardless of their location within the network.
- Automated DevSecOps Pipelines: Build CI/CD workflows that automatically fail builds if a high-severity vulnerability is detected or if an image is not signed by a trusted authority.
- Runtime Threat Detection: Configure and deploy monitoring agents that alert security teams the moment a shell is opened inside a production container or an unauthorized file is modified.
- Hardened Multi-tenant Environments: Set up high-level workload isolation using technologies like gVisor or Kata Containers to ensure that one compromised container cannot affect the entire host.
Preparation Plan
- 7–14 Days (The Sprint): This is for those already working with K8s security daily; focus on practicing the PSI exam environment and quickly reviewing curriculum gaps like runtime tools.
- 30 Days (The Standard): The most effective path for most professionals, dedicating 2 hours daily; spend the first two weeks on cluster hardening and the final two on supply chain and runtime security.
- 60 Days (The Deep Dive): Ideal for those transitioning from general SysAdmin roles; take this time to build local labs from scratch, break things manually, and understand the deep architectural “why” behind every security control.
Common Mistakes
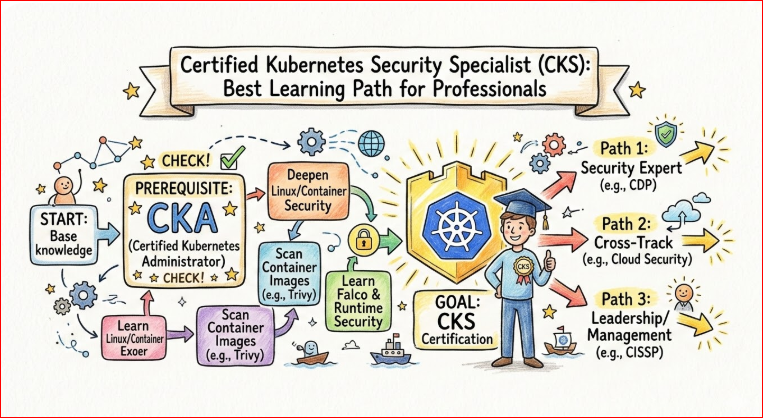
- Ignoring the Prerequisites: Many candidates forget that you must have a valid CKA (Certified Kubernetes Administrator) before you are even allowed to sit for the CKS exam.
- Poor Time Management: The exam is a 2-hour practical race; spending 20 minutes on a single complex Network Policy or Falco rule can easily cost you the entire certification.
- Terminal Inefficiency: Failing to master Vim, Tmux, or basic shell shortcuts can slow you down significantly in the high-pressure, command-line-only exam environment.
- Reliance on Search Engines: You cannot use Google; failing to practice navigating the official Kubernetes and Falco documentation sites will leave you stranded during the test.
Best next certification after this
After mastering Kubernetes security, the logical progression is moving toward a DevSecOps Professional track to master automation or a Cloud Security Architect certification to widen your scope. These paths allow you to take the deep technical skills from CKS and apply them to broader organizational strategy and compliance frameworks.
Comprehensive Certification Overview Table
| Track | Level | Who it’s for | Prerequisites | Skills Covered | Recommended Order |
| Kubernetes Security | Advanced | Security Engineers, SREs | CKA Certification | Hardening, Supply Chain, Runtime | 3rd (After KCNA, CKA) |
| Kubernetes Admin | Intermediate | DevOps, Cloud Eng | None (KCNA recommended) | Cluster Mgmt, Networking, Storage | 2nd |
| DevSecOps | Professional | Security Ops | Basic Linux & K8s | CI/CD Security, Vault, Compliance | 4th |
| SRE | Advanced | Platform Engineers | CKA | Reliability, Monitoring, SLIs/SLOs | 4th |
Choose Your Path: 6 Learning Tracks
1. The DevOps Path
This path focuses on the bridge between development and operations, where CKS ensures the “Operations” side of the house is fortified. You will learn to balance the need for rapid deployment with the necessity of a hardened infrastructure that prevents unauthorized configuration changes.
2. The DevSecOps Path
The most direct application of CKS skills, this track integrates security into every single phase of the software development lifecycle. You will focus on “Shifting Left” by securing the build and “Shielding Right” by monitoring the production environment for active threats.
3. The SRE Path
Reliability is impossible without security; an insecure cluster is fundamentally an unstable one prone to malicious disruptions. SREs use CKS knowledge to build resilient systems that can withstand both accidental failures and intentional attacks without dropping service levels.
4. The AIOps/MLOps Path
As AI models migrate to Kubernetes, securing the underlying data and the complex model training environments becomes a critical business requirement. CKS helps in isolating sensitive GPU workloads and ensuring that the high-value data processed by ML models is encrypted and protected.
5. The DataOps Path
This track focuses on the security and integrity of data pipelines moving through a containerized environment. By applying CKS principles, you ensure that data at rest and in transit within the cluster is strictly access-controlled and protected from unauthorized data exfiltration.
6. The FinOps Path
While FinOps is primarily about cost, security breaches are the most expensive “hidden costs” a company can face. Understanding K8s security allows you to optimize resource allocation without cutting corners that lead to costly compliance failures or insurance premiums.
Role → Recommended Certifications Mapping
| Job Role | Primary Certification | Specialization (CKS Focus) | Advanced / Leadership |
| DevOps Engineer | CKA (Administrator) | CKS (Security Specialist) | Jenkins Certified / ArgoCD |
| SRE | CKA (Administrator) | CKS (Security Specialist) | Prometheus & Chaos Engineering |
| Platform Engineer | CKA (Administrator) | CKS (Security Specialist) | HashiCorp Vault / Terraform |
| Cloud Engineer | AWS/Azure/GCP Solutions Architect | CKS (Security Specialist) | Multicloud Security Professional |
| Security Engineer | CKS (Security Specialist) | DevSecOps Professional | CISSP / CISM |
| Data Engineer | CKA (Administrator) | CKS (Security Specialist) | Databricks / Snowflake Security |
| FinOps Practitioner | Cloud Digital Leader | CKS (Security Awareness) | FinOps Certified Practitioner |
| Engineering Manager | KCNA (Fundamentals) | CKS (Technical Oversight) | CISM / PMP |
Top Institutions for CKS Training & Certification
DevOpsSchool
This is a premier institution offering deep-dive practical training that goes well beyond the exam syllabus. Their CKS program is led by industry veterans who bring decades of field experience, focusing on real-world scenarios and provide robust lab environments that perfectly mimic the actual exam setting.
Cotocus
Widely recognized for their “Learning by Doing” philosophy, Cotocus provides intensive bootcamps that are highly immersive. Their CKS training is updated frequently to keep pace with the latest Kubernetes versions, ensuring students are always learning the most current security patches and strategies.
Scmgalaxy
As a community-driven platform, Scmgalaxy offers an extensive repository of blogs, video tutorials, and technical resources. Their CKS mentorship programs are particularly highly rated for their focus on supply chain security and helping students master runtime protection tools like Falco.
BestDevOps
This institution offers highly tailored training sessions for both corporate teams and individuals. They excel at helping students understand how CKS skills fit into a broader, long-term DevOps career, focusing on the strategic integration of security into the overall business lifecycle.
Specialized Schools
- devsecopsschool.com: The go-to destination for those looking to pivot specifically into security-heavy roles with a focus on automation.
- sreschool.com: A specialized platform that bridges the gap between cluster reliability, performance tuning, and infrastructure security.
- aiopsschool.com: Provides a unique curriculum that tailors Kubernetes security specifically for the needs of AI, Machine Learning, and heavy data workloads.
- dataopsschool.com: Focuses on the intersection of data engineering and secure infrastructure, ensuring data integrity across complex pipelines.
- finopsschool.com: Offers a curriculum that emphasizes building secure cloud environments that are also optimized for cost and operational efficiency.
Next Certifications to Take
- Same Track: Advanced DevSecOps Professional – This allows you to dive even deeper into automated security testing, “Policy as Code,” and continuous compliance within the pipeline.
- Cross-Track: HashiCorp Certified: Vault Associate – Mastering external secrets management is the perfect technical complement to the internal security controls you learn in the CKS.
- Leadership: Certified Information Systems Security Professional (CISSP) – This is for those looking to transition from a technical specialist into high-level leadership roles like CISO or Security Director.
Testimonials
“Coming from a legacy infrastructure background, I thought I understood security, but the CKS shifted my entire perspective. The hands-on labs from DevOpsSchool were the key to my success in mastering container isolation.” – Ananya R., Senior Cloud Engineer
“As an Engineering Manager, I needed my team to be CKS certified to meet our strict global compliance goals. The training provided by Scmgalaxy made our transition to a security-first culture seamless and highly effective.” – Mark S., Engineering Lead
“The CKS isn’t just another badge on my profile; it was a fundamental transformation in how I think about code deployment. BestDevOps helped me master the complex Network Policies that usually trip up most candidates.” – Rajesh K., SRE
FAQs on CKS (Certified Kubernetes Security Specialist)
1. Is the CKS exam difficult?
Yes, it is widely considered one of the most challenging certifications in the ecosystem because it is 100% practical and requires a valid CKA as a prerequisite. You are tested on your ability to perform, not just your ability to remember.
2. How long does the CKS certification last?
The CKS certification is valid for 2 years, reflecting the rapid pace of change in the Kubernetes security landscape. This ensures that certified professionals are always up-to-date with the latest threat vectors and defense mechanisms.
3. Do I really need CKA before taking CKS?
Yes, the Linux Foundation strictly requires a current, non-expired CKA certification to be eligible for the CKS. This ensures that every candidate has a strong foundational knowledge of cluster administration before diving into security.
4. How much time should I dedicate to studying?
For a working professional with some K8s experience, 4-6 weeks of consistent study—about 10 to 12 hours per week—is usually the sweet spot for success. This allows enough time for both theory and extensive hands-on lab practice.
5. What is the format of the exam?
It is a performance-based exam taken in a browser-based terminal environment where you solve 15-20 real-world security tasks. You are required to interact with live clusters to fix vulnerabilities and implement security controls.
6. Can I use external notes during the exam?
No, you are strictly forbidden from using external notes or personal documentation. You are only allowed to access specific, white-listed official documentation sites like the Kubernetes and Falco documentation.
7. Does CKS help in salary hikes?
Absolutely; in both Indian and global markets, security-specialized Kubernetes engineers often command 30-50% higher salaries than general administrators. The scarcity of high-level security talent makes this a very lucrative certification.
8. What happens if I fail the first attempt?
Most exam purchases from the Linux Foundation include one free retake, which takes a lot of the pressure off the first attempt. However, it is always best to check the specific terms at the time of your purchase.
9. Is CKS relevant for Managers?
While managers may not need to write Network Policies daily, understanding the CKS curriculum is vital for making high-level architectural decisions. It provides the technical oversight needed to lead teams in highly regulated industries.
10. Which version of Kubernetes is used in the exam?
The exam environment usually tracks within one or two versions of the current stable Kubernetes release. It is important to check the official curriculum frequently as it is updated to reflect new features and security tools.
11. Are third-party tools like Falco or Trivy included?
Yes, the CKS curriculum specifically tests your ability to use popular open-source security tools to audit and secure your cluster. You must know how to install, configure, and interpret the outputs of these specific tools.
12. What is the passing score for the CKS?
Typically, you need a score of 67% or higher to pass the exam and earn the certification. This relatively high bar ensures that only those with a deep practical understanding of the material are certified.
FAQs on Certified Kubernetes Security Specialist (CKS)
1. How does CKS differ from CKA and CKAD? While CKA (Administrator) focuses on cluster management and CKAD (Application Developer) on deploying workloads, CKS is purely about security. It assumes you already know how to build and run a cluster and instead challenges you to protect it. You will spend less time on deployments and more time on Network Policies, Benchmarking, and Runtime monitoring.
2. Can I take the CKS if my CKA has expired? No. You must have an active, non-expired CKA certification to even register for the CKS exam. If your CKA is about to expire, I recommend renewing it first. The CKS acts as an “add-on” to your administrator credentials, validating that you can manage a cluster with a security-first mindset.
3. What is the most difficult domain in the CKS curriculum? Most engineers find Runtime Security and System Hardening to be the most challenging. Unlike standard Kubernetes objects, these require you to interact with the underlying Linux kernel and third-party tools like Falco or AppArmor. Mastering the configuration files for these tools is often where candidates lose the most points.
4. How is the CKS exam proctored and what is the environment like? The exam is conducted online and is proctored via webcam and screen sharing. You are provided with a remote Linux terminal in a browser. You must be comfortable working in a command-line environment (CLI) for two hours straight, as there is no graphical user interface (GUI) provided for cluster management.
5. Is the “Supply Chain Security” section relevant for DevOps engineers? Absolutely. In the 20-year span of my career, supply chain attacks have become a top threat. This section of the CKS teaches you how to ensure that only trusted, scanned, and signed images make it into your production environment. It is the “Shift Left” philosophy put into practical, technical practice.
6. What resources am I allowed to use during the actual exam? You are permitted to open one additional browser tab to access the official Kubernetes documentation, the Falco documentation, and the Trivy documentation. You cannot use any other external sites, blogs, or personal notes. Efficiency in searching these specific sites is a key skill for passing.
7. How much does the CKS certification help in career progression? In today’s market, “Kubernetes Security” is a high-demand, low-supply skill set. Holding a CKS often places you in a higher salary bracket and makes you a prime candidate for Lead DevSecOps or Senior SRE roles. It proves to employers that you can handle mission-critical, sensitive production data.
8. What happens if the Kubernetes version updates right before my exam? The Linux Foundation typically updates the exam environment within 4–8 weeks of a new Kubernetes stable release. It is vital to check the official curriculum page a week before your exam to see which version you will be tested on, as command flags and API versions can change between releases.
Conclusion
After twenty years in this field, I’ve seen many technologies come and go, but the need for robust, proactive security is the one constant. The Certified Kubernetes Security Specialist (CKS) is more than just a certificate; it is a rigorous validation of your ability to protect the digital assets of your organization in an increasingly hostile environment. Whether you are an engineer on the front lines or a manager steering the ship, mastering these security principles is the single best investment you can make in your professional journey.